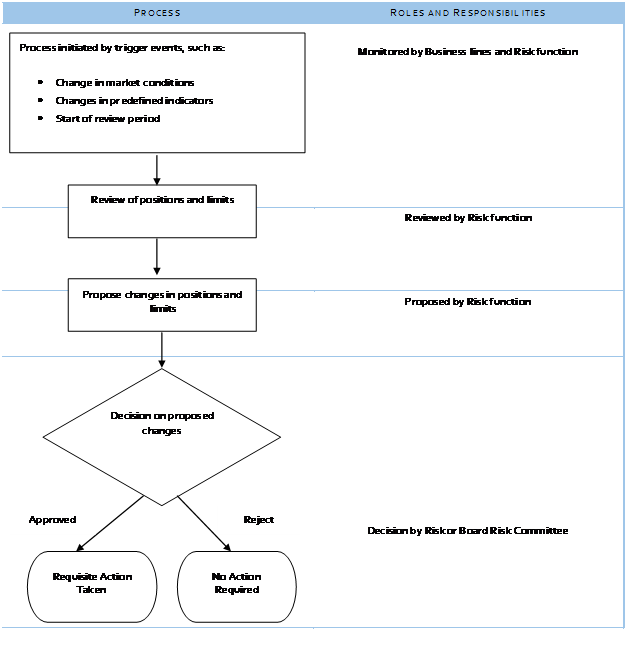
We next look at the Treasury limit setting workflow. For control and governance purposes the Treasury limit management function is kept under a separate group called the Middle Office with its own independent reporting line. The Middle Office function tracks and reviews treasury exposures on a day to day basis and technically in collaboration with the business users is expected to review limits whenever a change in market conditions requires it. Ideally, the Middle Office function should track core indicators such as risk, volatilities, exposures and expected loss and trigger the review process when these indicators breach pre-set limits, trends or bands. However, in well running functions while the Middle Office function may propose such changes they still need to be reviewed and approved by the appropriate risk committee before such changes can be enforced.
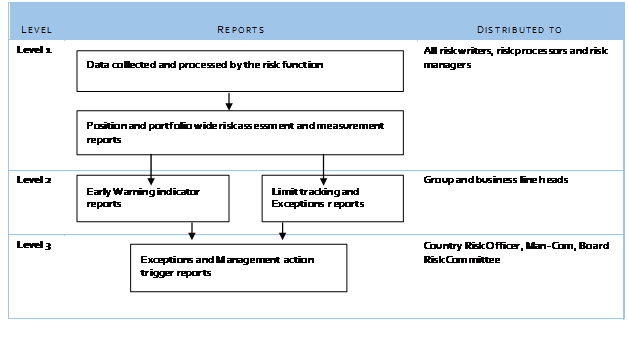
The next two diagrams do a quick walkthrough of the process
For the process to monitor and track target limits the reporting process needs to be set in such a fashion that early warning indicators, exception reports and management action triggers all get tracked and reported on a daily, weekly or monthly basis and the treasury, ALCO, Management committee teams are aware of how to work with the same. Within these reports, it is important that rather than generating and circulating 10 reports with 400 hundred indicators, well designed dashboard that highlight exceptions whenever they occur are used.
What are these exceptions? There are three primary categories.
- A range breach where a metric being tracked suddenly jumps above or below a historical range or a barrier. These breaches can occur at single or multiple points.
- Volatility breach where there is a sudden increase or decrease in underlying volatility.
- A systemic degradation where values for the metric being monitored fall below historical thresholds and stay there.
Good reporting systems make it easier to highlight exceptions when they occur rather than hide them in the volume of data and reports that are being produced.
Conclusion
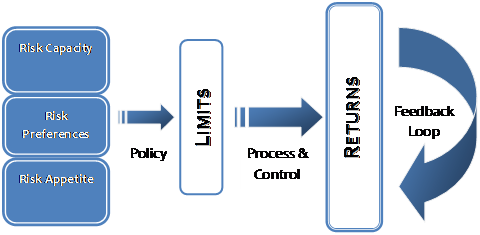
It is time to revisit the first image we presented when we started. The right risk management mindset is not driven by a single moving part. As we have seen above, it is driven by eight inter-related elements. For it to work, they all need to come together and work. If you get just one of these elements right (data or model or policy or process or limits or control) and miss the others, the approach will fail.